What is the TorProject
The TorProject is a pretty cool option to help you preserve your anonymity on the internet. Among other things, the Torproject created the Tor browser that allows you to surf without directly contacting the remote server. What your network administrator sees is that you are connected to a Tor Entry point server. The Tor network will then contact your destination server through one of many Tor Exit points. Just as your network administrator will not know which servers you are contacting, the destination server will not know what your source ip address is when you are using the Tor network.
Anonymity has its Problems
While the Tor network has a remarkable upside, there are some issues that it can present. Some of my other websites have been attacked by people using the Tor network to hide their identity. This leads to the network being distrusted and is unfortunate.
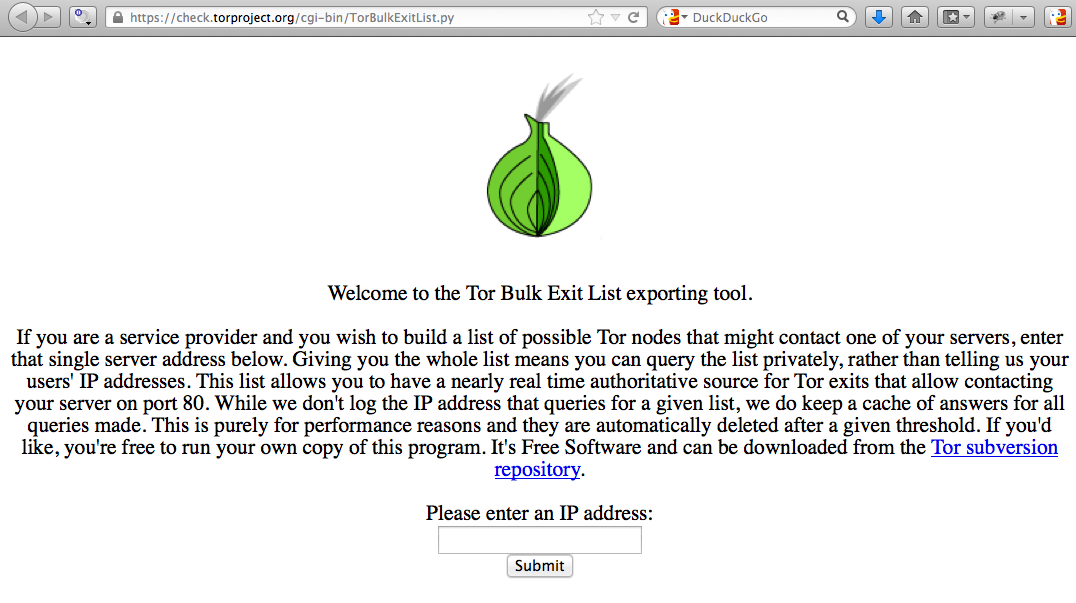
TorProject Exit List Exporter
Because of the issue that I had, I needed a way to protect my websites from the tor exit list, and to the Torproject’s credit, they provide one for you.
They have created a webpage that you can find at: https://check.torproject.org/cgi-bin/TorBulkExitList.py where you can type in your server’s ip address and it will give you the list of exit points that would be used to access your website. As this list is dynamic and can change, you need to get an updated list frequently.
Block Tor network exit nodes and Automate the List Download
To resolve my problem on my other machine, I simply created a small script that will get the exit list and add the exit points to my iptables firewall. Which you can see below. You are welcome to use my script which is listed below. Just put a comment in the comments section below and tell me how it works for you. I put the script below in a file at the path: /usr/local/sbin/gettorlist, then I ran chmod 700 /usr/local/sbin/gettorlist; chown root:root /usr/local/sbin/gettorlist.
| # Gets List of the Torproject Exit Points that would access your ipaddress # # This URL gets the new list: # URL=’https://check.torproject.org/cgi-bin/TorBulkExitList.py?ip=<ENTER YOUR IP ADDRESS HERE>‘ TORIPLIST=.toriplistGETTORLIST() { /usr/bin/wget –no-check-certificate –output-document=${TORIPLIST} ${URL} } # End of GETTORLIST BLOCKADDRESSES() for node in `/bin/grep -v -e ^# ${TORIPLIST}` } # End of BLOCKADDRESSES GETTORLIST rm -f ${TORIPLIST} |
Schedule with Crontab
Finally, I schedule it to run every hour or so with crontab. This way, I get constant updates to the list in my firewall. This has totally eliminated the attacks that I was getting from through the Tor network. You can see the Tor Exit List ip addresses in your iptables firewall by typing: “service iptables status”.
Latest posts by Jeff Staten (see all)
- Configure Your HP Procurve Switch with SNTP - May 5, 2015
- Configuring HP Procurve 2920 Switches - May 1, 2015
- Troubleshooting Sendmail - November 28, 2014


Works for me with little rework. Good job, thank you 🙂
Saved 45 minutes from my life with this.
My version:
#!/bin/bash
{
wget https://check.torproject.org/cgi-bin/TorBulkExitList.py?ip=YOUR_IP_HERE -O /etc/rc.d/torrs
}
BLOCKADDRESSES()
{
/usr/sbin/iptables -N TORBLOCK
/usr/sbin/iptables -F TORBLOCK
/usr/sbin/iptables -I TORBLOCK -j RETURN
for node in `/bin/grep -v -e ^# /etc/rc.d/torrs`
do
/usr/sbin/iptables -I TORBLOCK -s $node -j DROP
done
}.
BLOCKADDRESSES
Thanks so much for putting this up! It completely stopped an attack that was taking our entire company down earlier today!
Thanks for the explanation. I used it but I saw that it wasn’t blocking anything from the list, but everything was loading OK from the files into iptables..
I added this:
/sbin/iptables -D INPUT -j TORBLOCK
/sbin/iptables -I INPUT -j TORBLOCK
just after creating the TORBLOCK with the -N option… now it works perfectly.. the list wasn’t being called to process…